Workspace Security
Multi-layer security with OS-level sandboxing, workspace isolation, folder permissions, and credential protection.
The desktop app implements a multi-layer defense strategy to ensure AI agents operate safely within defined boundaries. Every layer works independently so that if one is bypassed, the others still protect your system.
Defense Layers
Layer 1: Input Validation
All inputs are validated before reaching the agent:
- Path traversal blocking -- Rejects attempts to escape the workspace directory
- System path blocking -- Blocks access to OS system directories
- Schema validation -- Every input is checked against strict rules
Layer 2: OS-Level Sandbox
The strongest boundary -- enforced by the operating system itself:
| Platform | Description |
|---|---|
| macOS | Kernel-level sandbox restricting file and network access |
| Linux | Container-like isolation with namespace restrictions |
The sandbox enforces filesystem rules:
- Allowed: Writing to session directory + optionally your workspace
- Blocked for writing: Shell configs, credential stores
- Blocked for reading: Credential directories (SSH keys, AWS credentials, GPG keys, etc.)
Layer 3: System Prompt Boundaries
The agent's instructions define operating zones:
- Which directories the agent can access
- What types of operations are permitted
- Backup-before-overwrite and read-before-write requirements
Layer 4: Folder Permission Consent
A permission model where you control access:
- When the agent needs access to a folder, a dialog appears
- You choose: Once, Today, Always, or Never
- Non-permanent permissions reset on app restart
- Each folder tracks its read/write permission state
Layer 5: Command Validation
Before the agent runs any shell command:
- Paths are validated against the workspace boundary
- Commands are checked against an allowlist
- Dangerous operations are blocked
Workspace Isolation
How Workspaces Work
Every task operates within a defined workspace:
- Session directory -- Always writable, used for agent output
- User workspace -- Your project folder, read-only by default
To give the agent write access to your project:
- Select a folder using the folder picker
- Grant write permission when prompted
- The agent can now modify files in that folder
Multi-Folder Workspace
A single task can access multiple directories:
- When creating or continuing a task, add additional folders via the folder picker
- Each folder requires its own permission grant
- The agent can read and write across all granted folders
- All folders are subject to the same sandbox and permission rules
Folder Permissions
The folder permission system tracks:
| Permission | What It Means |
|---|---|
| Read | Agent can view file contents |
| Write | Agent can create and modify files |
| Once | Permission expires after this task |
| Today | Permission expires at end of day |
| Always | Persists across sessions |
| Never | Blocks access completely |
Recent folders are tracked for quick access in the folder picker.
Sandbox Status Badges
In Settings > Workspace, sandbox choices show a status badge:
| Badge | What It Means |
|---|---|
| Hard | Designed for untrusted work with strong isolation |
| Reduced | Some isolation is active, but extra safety limits still apply |
| No isolation | Runs directly on your computer and should only be used for trusted local work |
The Native option is marked No isolation. Use it only when you trust the command or script you are running.
Credential Protection
The app protects sensitive credentials at multiple levels:
Encrypted Storage
OAuth tokens and API keys are encrypted at rest using industry-standard encryption (AES-256-GCM with strong key derivation). Each credential is encrypted independently with its own unique parameters.
Slack App Home credentials add another layer: each paired Slack user gets a separate encryption key. If that user disconnects, Neumar deletes the wrapped key so saved personal tokens and MCP headers can no longer be decrypted.
Protected Directories
The sandbox explicitly blocks agent access to sensitive directories:
- SSH keys
- AWS credentials
- GPG keys
- Git credentials
- Package manager tokens
Git Staging Filters
When creating pull requests (via the Linear Pipeline), the staging process automatically excludes:
- Environment files (
.env) - Key and certificate files
- Other known sensitive file patterns
Link Safety
When an AI agent includes links in its responses, clicking any external link triggers a confirmation dialog before opening it. This protects you from accidentally visiting malicious or unexpected URLs that may appear in AI-generated content.
The dialog shows:
- The full URL so you can verify where the link leads
- A Copy link button to copy the URL without opening it
- An Open link button to proceed and open the link in your default browser
This applies consistently across all message views -- home screen chat, task detail, and the V2 streaming thread.
App Permissions
The desktop app restricts its own permissions to only what's needed:
| Capability | Scope |
|---|---|
| File System | Read/write scoped to app data and user directories |
| Database | Local database operations only |
| Processes | Spawn/manage agent processes |
| Dialogs | Native folder/file picker |
| Notifications | OS notifications for task completion |
| URLs | Open links and files in default apps |
Network Security
- Origin restrictions -- Only authorized sources can communicate with the app
- Request size limits -- Prevents oversized payloads
- URL validation -- User-supplied URLs are validated to block access to private networks (private IPs, cloud metadata endpoints, and non-HTTPS schemes are rejected)
- Self-hosted media checks -- Immich and PhotoPrism connections can use explicit local network URLs, but the app still blocks cloud metadata hosts, embedded credentials, unsafe redirects, and non-HTTPS public URLs
- LAN path mapping checks -- Cloud storage path mappings must point to real local directories and are verified before the app reads files through them
- Model endpoint validation -- Custom AI model base URLs are checked against the same rules to prevent misuse
- Redirect checks -- Network requests are checked again after redirects, so a public-looking link cannot quietly redirect to a private address
- Marketplace checks -- Plugin marketplace registries are validated before they are loaded and cached
Tool Output Protection
Tool results are checked before they are shown to the agent again. This helps stop malicious web pages, files, or tool responses from sneaking in instructions such as "ignore previous instructions" or requests to leak credentials.
When suspicious output is detected, the app can:
- Show a warning
- Replace the unsafe output before the agent sees it
- Block the output from continuing through the task
- Record a redacted security event for review
The app does not store raw secrets in these security records.
Security Events
The app records redacted security events when it blocks or flags risky behavior, such as unsafe network destinations, canary-token leaks, reduced sandbox isolation, or blocked tool output. These records are designed for troubleshooting and do not include raw API keys, raw credentials, or full sensitive payloads.
Remote and Channel Access
Remote and channel features add extra controls before outside clients can reach your agent:
- Remote access requires login -- WebUI and remote viewer connections use password-based login with short-lived access tokens and rotating refresh tokens
- Read-only remote mode -- The current remote viewer can show recent tasks and live updates, but it cannot send prompts, approve actions, or change settings
- Agent discovery is public -- If you expose the app to a network, the public agent discovery card can reveal active agent profile names and descriptions
- Channel user controls -- Bot channels can be open for personal use or require pairing before new users can run agent tasks
- Channel rate limits -- Messaging and agent-client protocols apply per-user limits to reduce abuse and accidental loops
Background Daemon Safety
The Run in background option installs a native supervisor so the sidecar can keep running after the desktop window is closed. The app validates the supervisor name and sidecar path before installation, escapes values written into OS templates, and only reads the app's own sidecar log from ~/.neumar/logs/sidecar.log.
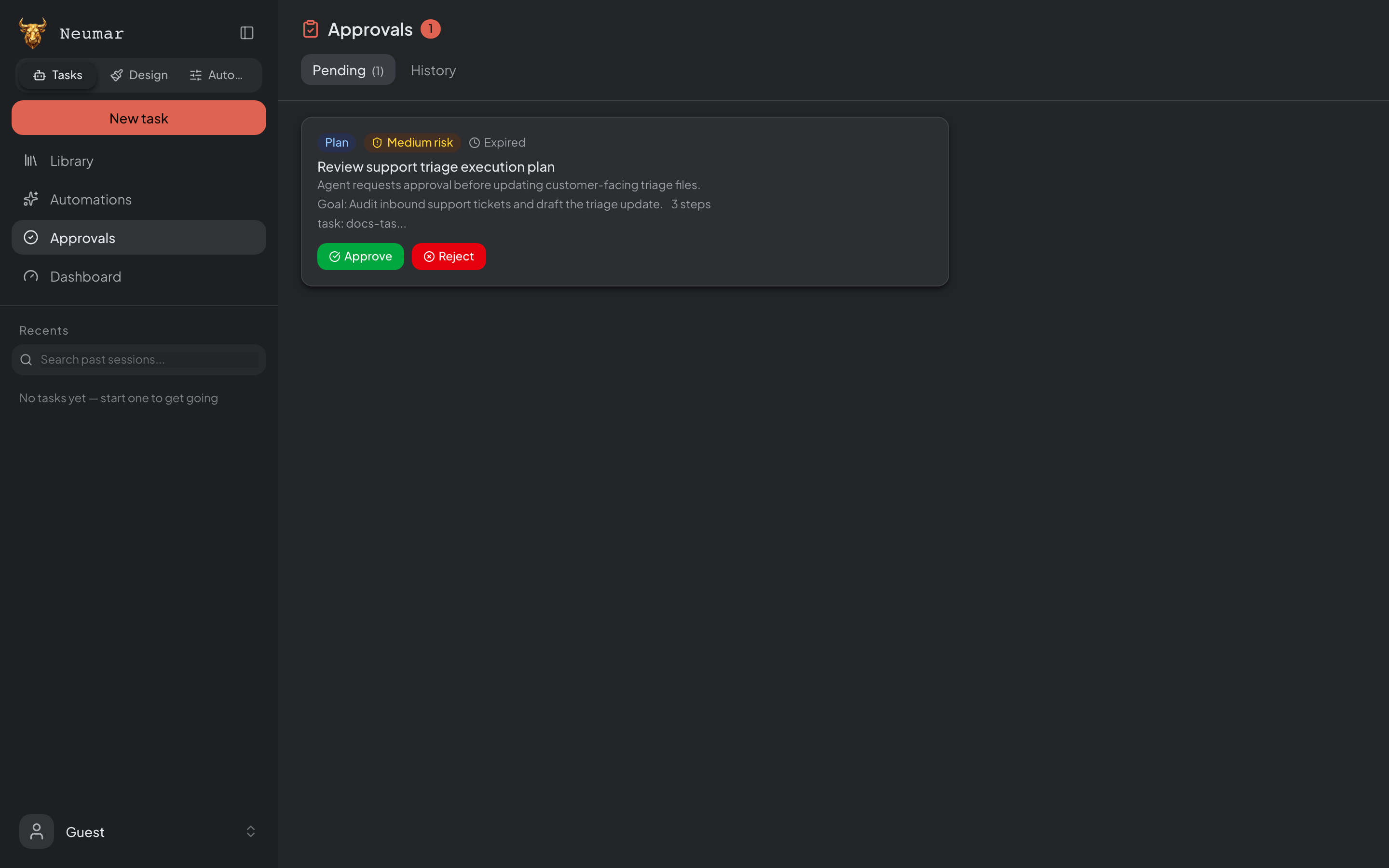
Tool Permission System
Beyond workspace isolation, the app includes a tool-level permission system that controls what the agent can do during execution.
How It Works
Every tool the agent calls is classified by risk level:
| Classification | Examples | Default Behavior |
|---|---|---|
| Read | Viewing files, searching code | Auto-approved |
| Write | Creating or editing files | Auto-approved |
| Execute | Running shell commands | Requires your approval |
| Network | Web searches, API calls | Requires your approval |
When a tool requires approval, a permission dialog appears with three options: Deny, Allow Once, or Always Allow.
Dangerous Action Detection
The app scans tool inputs for risky patterns before execution:
- Blocked automatically: Destructive disk operations, credential exfiltration attempts
- Flagged for review: Using sudo, changing file permissions broadly, killing processes
- Sensitive path protection: Writing to system directories or credential stores is blocked
Denial Tracking
If you deny the same tool request three or more times, the app guides the agent to try a different approach -- preventing frustrating retry loops.
AI Safety Review (Optional)
An optional AI-powered safety layer provides an independent second opinion on tool calls classified as potentially sensitive. When enabled:
- A fast automated check runs before executing risky tools (under 2 seconds)
- If the check is inconclusive, a deeper analysis runs (under 5 seconds)
- Results are cached so the same action isn't re-checked
- If a concern is flagged, you'll see a standard permission dialog
This feature is off by default. Enable it in Settings to add an extra layer of safety for your workflow.
Tool Lifecycle Hooks
You can set up custom hooks that run before or after any tool execution:
- Pre-Tool-Use hooks can allow, block, or modify tool actions
- Post-Tool-Use hooks run after execution for logging or auditing
- Hooks target specific tools via pattern matching (e.g.,
Bash,Write|Edit) - All hooks fail open -- if a hook encounters an error, it won't block the agent
Configure hooks in Settings > Hooks.
Output Size Protection
The app automatically truncates oversized tool outputs to keep the interface responsive. Full output is always available in your workspace -- only the display is trimmed. This prevents a single large result from overwhelming the conversation view.
Agentic Security
The app addresses the major security concerns for AI agent applications:
| Concern | How It's Handled |
|---|---|
| Goal hijacking | Prompt boundaries prevent instruction override |
| Tool misuse | OS-level filesystem sandbox + tool permission system |
| Privilege abuse | No auto-merge, scoped operations, credential denial |
| Excessive agency | Workspace boundaries, session confinement |
| Unsafe code execution | Verification loop (lint + type-check, max 3 retries) |
| Insufficient isolation | OS-level enforcement + protected directories |
| Cascading failures | Per-phase timeouts, total pipeline timeout |
| Trust exploitation | No auto-merge, explicit human review required |
Learn More
- Agent System -- How agents operate within these boundaries
- Linear Pipeline -- Security in the autonomous workflow
- Desktop Application -- Overview and setup